
Quantum Cloning Breakthrough has got the quantum world rethinking the limits of quantum information. Read here to learn more about quantum cloning.
Recent experimental advances claiming the creation of “perfect copies” of quantum states have sparked significant interest in the scientific community.
At first glance, this appears to challenge one of the most fundamental principles of quantum mechanics, the No-Cloning Theorem.
However, a deeper analysis reveals that rather than violating this law, researchers have devised an innovative framework that works within its boundaries while unlocking new possibilities for quantum technologies.
Understanding the No-Cloning Theorem
The No-Cloning Theorem is a cornerstone of quantum mechanics. It states that an unknown quantum state cannot be copied perfectly.
This limitation arises due to the nature of quantum systems:
- Quantum information exists in superposition, where particles can exist in multiple states simultaneously.
- Any attempt to measure or duplicate this state leads to wavefunction collapse, governed by Quantum Measurement.
- Unlike classical bits, which can be copied freely, quantum bits (qubits) cannot be duplicated without disturbing the original information.
This principle has far-reaching implications:
- It ensures the security of quantum cryptography, particularly Quantum Key Distribution.
- It imposes constraints on quantum computing architectures, especially in data storage and error correction.
Quantum cloning
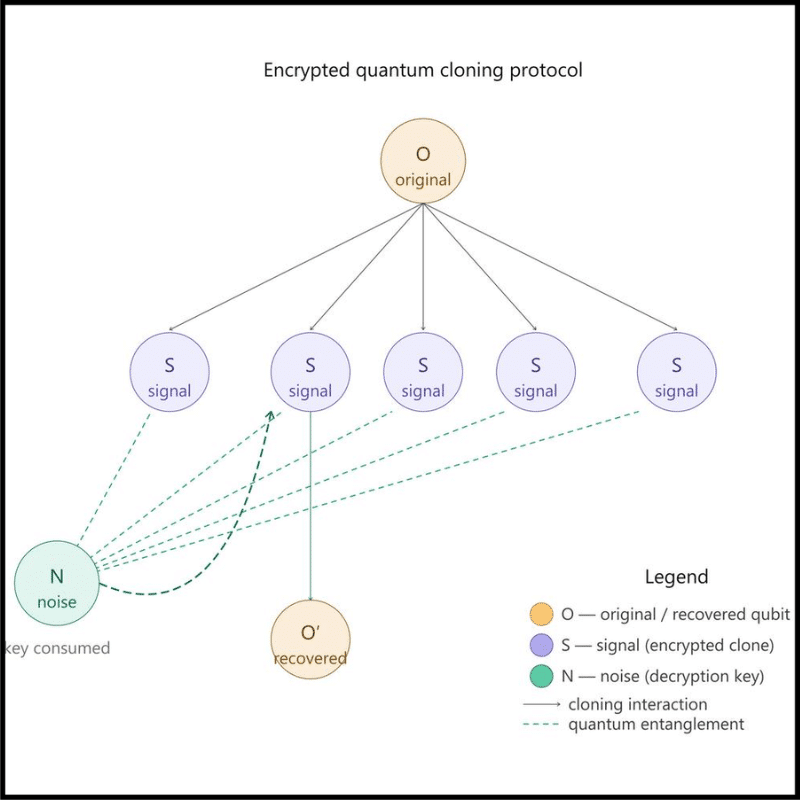
The recent breakthrough introduces a clever workaround that respects the theorem while enabling a form of controlled duplication.
- Encryption-Based Quantum Distribution
Instead of directly copying a quantum state, researchers:
- Distribute the original quantum information across multiple qubits
- Encode each fragment using quantum noise, making it appear random
- Use special “noise qubits” as decryption keys
Each copy is incomprehensible on its own, resembling random noise. Only with the correct key can the original state be reconstructed.
This method draws conceptual parallels with:
- Quantum Error Correction
- Quantum Secret Sharing
- The One-Time Recovery Constraint
A defining feature of this approach is the single-use nature of reconstruction:
- The decryption key can recover only one perfect copy of the original quantum state
- Once used, the key is irreversibly destroyed
- All other encoded copies become permanently unreadable
Thus, while multiple encoded “copies” exist, only one usable instance can ever be realised, preserving the spirit of the no-cloning theorem.
Strategic Significance of the Breakthrough
- Revolutionising Quantum Cloud Storage
One of the biggest challenges in quantum systems is data fragility. This method enables:
- Redundant storage of quantum information across distributed servers
- Recovery of data even if several nodes fail
- A foundation for fault-tolerant quantum cloud infrastructure
- Advancing Fault-Tolerant Quantum Computing
Quantum computers are highly sensitive to environmental disturbances. The new approach:
- Enhances data reliability and recovery mechanisms
- Complements ongoing work in Quantum Computing
- Brings us closer to scalable and practical quantum machines
- Ultra-Secure Communication Systems
Security is inherently built into this framework:
- All stored states appear as random noise without the key
- Even intercepted data is unusable
- Offers stronger protection than many classical encryption systems
This reinforces the foundations of next-generation secure communication.
- Enabling Precision and Personalised Technologies
By leveraging controlled reconstruction:
- It may support precision simulations in medicine and material science
- Could enable highly secure data sharing frameworks across sensitive sectors like defence and finance
Conceptual Interpretation: A New Way to Think About Information
This development reframes our understanding of quantum information:
- Traditional View: “Quantum information cannot be copied.”
- Revised View: “Quantum information can be securely distributed and reconstructed once.”
This subtle shift has profound implications. It suggests that while perfect duplication remains impossible, practical redundancy and recovery are achievable.
Challenges and Limitations
Despite its promise, several hurdles remain:
- Technological Complexity: Implementing noise-based encryption at scale is highly demanding
- Resource Intensity: Requires large numbers of qubits and precise control
- Error Sensitivity: Quantum systems remain vulnerable to decoherence
- Scalability Issues: Translating laboratory success into real-world infrastructure will take time
Way Forward
To harness this breakthrough effectively, the following steps are essential:
- Investment in Quantum R&D: Strengthening research ecosystems and infrastructure
- Development of Quantum Networks: Building distributed architectures for storage and communication
- Global Collaboration: Sharing knowledge across countries and institutions
- Regulatory Frameworks: Ensuring ethical and secure deployment of quantum technologies
Conclusion
The recent development does not overturn the No-Cloning Theorem but rather demonstrates the ingenuity of working within its constraints. By enabling encrypted, single-use reconstruction of quantum states, it opens a new frontier in quantum science.
This breakthrough has the potential to transform quantum computing, secure communication, and cloud infrastructure, marking a significant step toward a future where quantum technologies are both practical and reliable.
Related articles:





Leave a Reply